To get to grips with biometric data and GDPR compliance, we first need to answer a fundamental question: what exactly is biometric data? It's not just any personal information. We're talking about data pulled from unique physical or behavioural traits—like a fingerprint, an iris pattern, or even someone's voice—that can unambiguously identify a specific person.
Think of it as a biological key, one that is unique to an individual and virtually impossible to change.
Defining Biometric Data Under GDPR
Under the General Data Protection Regulation (GDPR), what makes something "biometric data" isn't the type of data itself (like a photo), but the purpose for which you're processing it. A simple photograph of an employee on their ID badge isn’t automatically considered biometric data.
However, the moment that same photograph is fed into a facial recognition system to grant access to a building, it becomes biometric data. The legal framework completely changes.
The critical factor is the "specific technical processing" used for the purpose of unique identification. Getting this distinction right is the cornerstone of understanding your compliance obligations. You can dig deeper into the nuances in our guide on the processing of biometric data explained.
Why GDPR Treats Biometric Data Differently
Biometric data is classified as a ‘special category of personal data’ under Article 9 of the GDPR. This classification puts it in the same high-risk group as information about:
- Racial or ethnic origin
- Political opinions
- Religious or philosophical beliefs
- Health or sex life
This elevated status is there for a good reason: a breach involving biometric data has irreversible consequences. Unlike a password, you can’t just change your fingerprint or your iris. If this data is compromised, it creates a permanent risk of identity theft and fraud for that person.
To provide a clearer picture, here's a breakdown of common biometric data types and their status under the GDPR.
| Biometric Data Types and Their GDPR Classification | ||
|---|---|---|
| Biometric Identifier | Example Application | GDPR Special Category Status |
| Fingerprints | Unlocking a company phone, employee time-tracking | Yes, when used for unique identification. |
| Facial Recognition | Security access control, identity verification on a banking app | Yes, when used for unique identification. |
| Iris/Retina Scan | High-security facility access | Yes, when used for unique identification. |
| Voice Patterns | Authenticating a user for a secure service over the phone | Yes, when used for unique identification. |
| Keystroke Dynamics | Behavioural verification for fraud detection on a platform | Yes, when used for unique identification. |
| Gait Analysis | Security surveillance to identify individuals by their walk | Yes, when used for unique identification. |
As the table shows, the consistent theme is the use of this data for unique identification, which automatically triggers the special category protections under Article 9.
The Dutch Regulatory Approach
Here in the Netherlands, the Dutch Data Protection Authority (Autoriteit Persoonsgegevens or AP) enforces a particularly strict interpretation of these rules. Their guidance on facial recognition technology, for example, makes it crystal clear that its use is prohibited in most circumstances.
The key test is always whether the processing is intended to unambiguously identify a natural person. This strict stance underlines just how compelling your legal justification needs to be before you even consider implementing such a system.
Finding Your Lawful Basis for Processing Biometric Data
When you're dealing with biometric data, the GDPR essentially makes you clear two separate legal hurdles. It's not a case of just finding one good reason to process the data. You need a lawful basis under Article 6 for general processing, and then a second, much stricter condition from Article 9 because you're handling 'special category' data. This two-part requirement is absolutely non-negotiable.
Think of it like a bank vault with two different locks. Article 6 is the first key, the one you need for any kind of personal data processing. But because biometrics are so sensitive, Article 9 requires a second, more specialised key before you can even think about opening the door.
The Two-Key System of GDPR Compliance
First, you need to ground your processing in one of the six lawful bases from Article 6. These are the usual suspects: consent, contractual necessity, a legal obligation you have to meet, vital interests, performing a public task, or your own legitimate interests.
Once you’ve nailed down your Article 6 basis, the real challenge begins. You must also satisfy one of the specific conditions listed in Article 9(2), which are the only gateways for processing special category data. For biometrics, the most famous—and most frequently misunderstood—condition is explicit consent.
Deconstructing Explicit Consent
Don’t confuse ‘explicit consent’ with the standard consent you might use for a marketing newsletter. This is a much higher bar. It can’t be bundled away in your terms and conditions or implied from someone's actions. It has to be a crystal-clear, positive action that is:
- Specific: You can't just ask for a vague consent for "security purposes." You need to spell out precisely why you need the biometric data.
- Informed: People must know exactly what data you're collecting, what you'll do with it, who gets to see it, and how long you'll keep it.
- Freely Given: This is where it gets tricky, especially in the workplace. An employee might feel pressured to agree to a biometric system, fearing negative consequences if they refuse. That power imbalance means their consent isn't truly 'freely given' and is therefore legally invalid.
The Dutch AP (Autoriteit Persoonsgegevens) is extremely sceptical of using consent as a basis for processing employee biometric data. The authority's starting point is that such consent is almost never freely given and, as a result, fails to meet the GDPR's stringent requirements.
This is a crucial point for businesses in the Netherlands. Relying on employee consent for a biometric time clock or an office access system is almost always a compliance dead end. You need to look for stronger, more appropriate legal grounds.
Beyond Consent: Exploring Other Article 9 Exceptions
While explicit consent grabs all the headlines, Article 9 does offer a few other, very narrow, exceptions that might justify using biometric data. It's vital to be sure that your specific situation fits perfectly within one of these conditions, because getting it wrong can lead to serious trouble. Every business will need to carefully assess its role and responsibilities, which you can read about in our detailed explanation of a controller and a processor under GDPR.
To make this clearer, let's compare the most relevant conditions and their strict requirements.
Lawful Basis Comparison for Biometric Data Processing
The table below breaks down the common Article 9 conditions you might consider, highlighting where they work and where they often go wrong.
| Article 9 Condition | Key Requirement | Practical Example | Common Pitfall |
|---|---|---|---|
| Explicit Consent | Must be specific, informed, unambiguous, and freely given. | A customer voluntarily enrolling in a facial recognition payment system at a shop, with a clear and easy opt-out available. | Relying on employee consent, where the inherent power imbalance almost always invalidates it. |
| Employment Law | Processing is necessary to carry out obligations or rights in the field of employment or social security law. | Using fingerprints to access a highly sensitive laboratory, where this is mandated by specific health and safety legislation. | Using biometrics for general convenience (like time tracking) when less intrusive methods would do the job just as well. |
| Substantial Public Interest | Must be based on Dutch or EU law and be proportionate to the aim being pursued. | A law enforcement agency using facial recognition to investigate a serious crime, under a specific legal mandate from the government. | A private company trying to claim "public interest" for its own commercial security without any actual basis in Dutch law. |
| Vital Interests | Necessary to protect the vital interests of a person who is physically or legally unable to give consent. | Using a fingerprint scanner to identify an unconscious patient in an emergency to access their life-saving medical records. | Applying this basis to routine situations where the individual is perfectly capable of giving or withholding consent. |
In the end, choosing the right lawful basis isn't about picking the easiest option. It demands a thorough, documented analysis of your specific circumstances. Simply grabbing the one that seems most convenient is a fast track to non-compliance and a potential knock on the door from the Dutch AP.
How to Conduct a Data Protection Impact Assessment
If your organisation is even considering processing biometric data on any real scale, then a Data Protection Impact Assessment (DPIA) isn't just a good idea—it's a legal must under the GDPR.
Think of a DPIA as a formal privacy risk assessment. It's a structured process that forces you to map out exactly what you plan to do, spot the potential dangers for individuals, and figure out how to manage those risks before you ever scan a single fingerprint or face.
This is far more than a simple box-ticking exercise. It's a fundamental part of demonstrating accountability and baking data protection into the very design of your systems. For any high-risk activity like biometrics, the Dutch Data Protection Authority (AP) will absolutely expect to see a comprehensive and well-reasoned DPIA if they ever come asking questions.
Before you can even begin a DPIA for biometrics, you first have to clear two fundamental legal hurdles, as the diagram below shows.
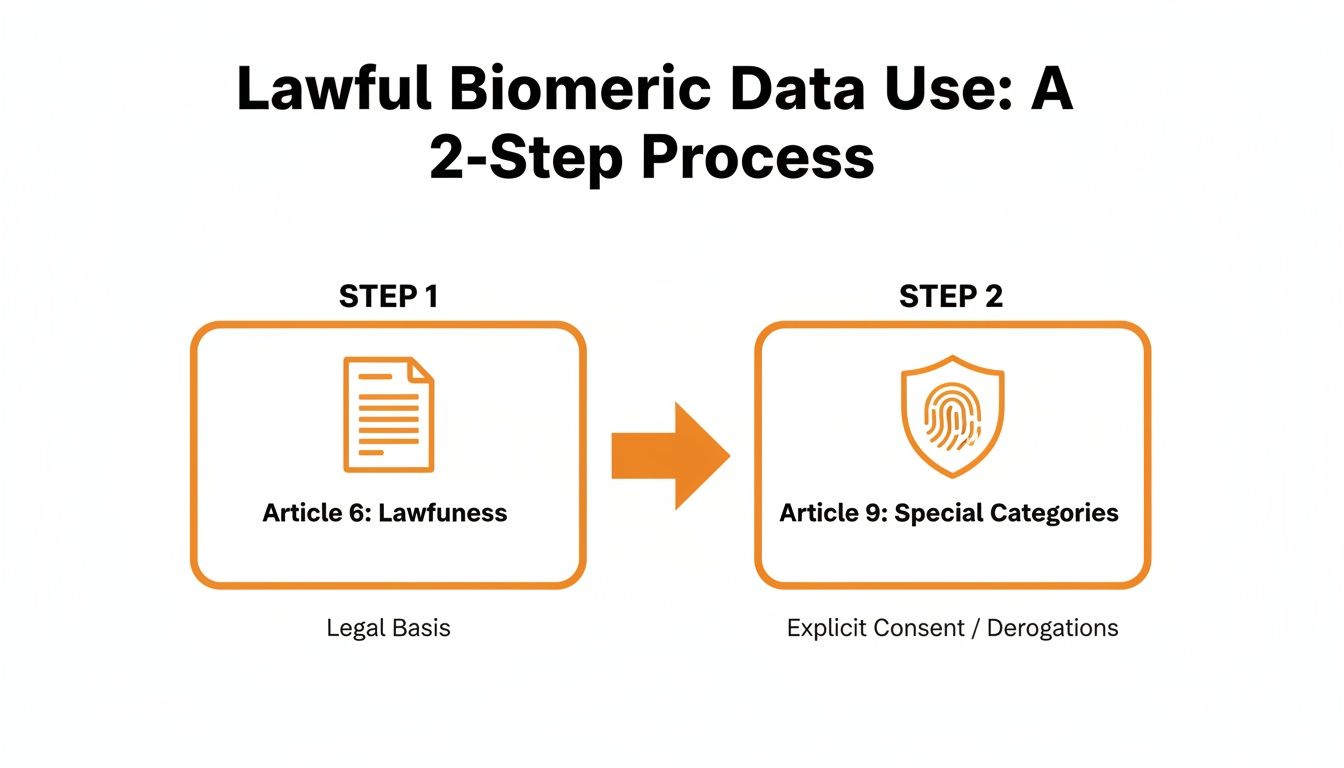
You must first find a lawful basis under Article 6 and then satisfy one of the strict, specific conditions under Article 9. Only then can you move forward with your assessment.
The Core Components of a DPIA
A solid DPIA needs to systematically describe the processing, assess why it's necessary and proportionate, and manage the risks to people's rights and freedoms. Let's walk through the key steps using a very common scenario: installing a fingerprint scanner for office access control.
-
Describe the Processing: Get specific. You need to detail the entire journey of the data from start to finish.
- What exactly are you collecting? (e.g., fingerprint templates, not the full images).
- How will this data be collected, where is it stored, how is it used, and when will it be deleted?
- Who can access this data, and why?
- Are any third-party vendors involved, like the company that supplied the scanner system?
-
Assess Necessity and Proportionality: This is where you justify your decision. It requires you to challenge your own assumptions and prove that using biometrics is the most sensible choice.
- What precise problem are you trying to fix? (e.g., preventing unauthorised access to server rooms).
- Why are less intrusive methods, like secure key cards or PIN codes, not good enough for this specific situation?
- Is the data you’re collecting truly the minimum required to achieve your goal?
-
Identify and Assess Risks: Put yourself in the shoes of an employee. What could possibly go wrong for them?
- Data Breach: What is the real-world impact if the database of fingerprint templates gets stolen?
- Function Creep: Is there a risk this data could be used for other things down the line, like monitoring when employees arrive and leave, without telling them?
- Exclusion: What happens if an employee can't use the system because of a skin condition or worn-down fingerprints? Is there an alternative for them?
- Inaccuracy: What if the system glitches and locks an authorised person out during a fire alarm?
-
Identify Measures to Mitigate Risks: Now, for every risk you've just listed, you need to propose a concrete solution. This is the most practical part of the process.
- Technical Measures: This could mean implementing strong encryption for the data, using secure template storage (on-device is often preferable to a central server), and enforcing strict access controls.
- Organisational Measures: This involves creating a clear policy on biometric data, training staff on it, and having a specific data breach response plan ready for this system.
- Proportionality Measures: Always offer a non-biometric alternative for access where possible. This ensures the system doesn't unfairly exclude anyone.
A well-executed DPIA is a living document. It's not something you do once and then file away. It should be reviewed and updated if the scope, nature, or context of your biometric processing changes. It serves as your primary proof of due diligence if a regulator ever questions your practices.
By following this structure, a DPIA changes from a daunting legal obligation into a powerful strategic tool. It helps ensure your use of biometrics is built on a solid foundation of foresight and responsibility, protecting both your organisation and the very people whose data you're processing.
Essential Steps for Day-to-Day Compliance
Getting your GDPR compliance right for biometric data isn’t a one-off legal chore you can tick off a list. It's an ongoing commitment that has to be woven into the fabric of your daily operations. Once you’ve sorted out your lawful basis and finished a DPIA, the real work of managing this sensitive data responsibly truly begins. It’s all about turning legal principles into practical, everyday actions.
At the heart of this is making sure the core principles of the GDPR become your company's default setting. A great place to start is with data minimisation. It’s a simple but incredibly powerful idea: only collect the biometric data you absolutely need for the specific, legitimate purpose you’ve identified. Nothing more. If you're setting up an office access system, do you really need a high-resolution facial scan when a much simpler biometric template would do the job just as well? Probably not.
This goes hand-in-hand with storage limitation. Biometric data shouldn't be kept forever. You need to establish and enforce clear retention policies. These rules should state exactly how long you'll store the data and ensure it's securely deleted the moment it's no longer needed for its original purpose.
Implementing Technical and Organisational Safeguards
Protecting biometric data properly demands a multi-layered security strategy. This means bringing together both technical solutions and solid internal policies. These aren't just nice-to-haves; they are non-negotiable requirements under the GDPR.
Here are some key technical measures you should have in place:
- Strong Encryption: All biometric data must be encrypted, period. This applies both when it’s stored on servers or devices (at rest) and when it's being sent across a network (in transit). Encryption makes the data unreadable and useless to anyone who might get their hands on it without authorisation.
- Strict Access Controls: Not everyone in your organisation needs to see or handle biometric data. Use role-based access controls to lock things down, ensuring only authorised staff with a clear, legitimate need can ever access this information.
- Secure Storage: Whenever you can, avoid storing biometric templates in one big central database. A much safer approach is to store them locally on a device, like the scanner itself or an employee's access card. This decentralised model dramatically lowers the risk of a catastrophic mass data breach.
But technology alone isn't enough. Your organisational measures are just as vital. Implementing robust security measures, like those found in biometric-first approaches to security, can seriously reduce fraud risk and strengthen your overall compliance. This also means regularly training staff on data protection policies and running periodic security audits to find and fix vulnerabilities before they become a problem.
Creating Transparent and Clear Privacy Notices
Transparency is a cornerstone of the GDPR. People have an absolute right to know exactly what you’re doing with their biometric data. Your privacy notice can’t be a dense, jargon-filled document buried in the footer of your website. It has to be clear, concise, and easy for anyone to find and understand.
A compliant privacy notice for biometric data processing must clearly explain:
- Who you are: Your company's name and contact details.
- Why you are processing the data: The specific, legitimate reason (e.g., "to secure access to our research lab").
- Your legal basis: The specific Article 6 and Article 9 conditions you are relying on.
- What data is being collected: Be precise. Don't just say "biometrics"; specify if it's a fingerprint template, an iris scan, etc.
- How long you will keep it: Your data retention period.
- Who you will share it with: This includes any third-party tech providers.
- Their rights: Let them know about their right to access, correct, erase, and object to the processing of their data.
Example of Clear Language: "We use a fingerprint template, which is a secure numerical representation of your fingerprint, to grant you access to the server room. This template is stored only on your personal access card and is deleted from our system within 24 hours of your employment ending. You can request to see or delete your data at any time."
This kind of clarity does more than just tick a legal box—it builds trust. When you're upfront and transparent about how you handle someone's most personal information, you show a commitment to data protection that goes beyond simple compliance. It turns a legal requirement into a cornerstone of your organisation's integrity.
Navigating Enforcement and Penalties in the Netherlands
Ignoring the GDPR's strict rules on biometric data isn't just a theoretical risk; it carries severe financial and reputational consequences. In the Netherlands, the Data Protection Authority (Autoriteit Persoonsgegevens or AP) is known for its firm enforcement. This makes the potential fallout from mishandling data a critical factor for any organisation to consider.
Understanding this enforcement landscape is essential. The potential penalties aren't just abstract legal threats. They are a reality that highlights just how important proactive compliance really is. The investment in getting your data processing right is invariably far less than the steep cost of getting it wrong.
The Real Cost of Non-Compliance
Under the GDPR, supervisory authorities like the Dutch AP have the power to impose substantial fines. These penalties are designed to be effective, proportionate, and dissuasive, reflecting how seriously they view the infringement. For severe violations, like processing special category data without a valid legal basis, the fines can be staggering.
Organisations can face penalties of up to €20 million or 4% of their total worldwide annual turnover from the previous financial year, whichever is higher. This two-tiered system ensures that the fines have a significant impact on even the largest global corporations.
The message from regulators is crystal clear: mishandling biometric data is one of the most serious breaches of data protection law. The financial penalties are structured to ensure that non-compliance is never a financially viable option for any business, regardless of its size.
High-Profile Enforcement in the Netherlands and EU
Recent actions from the Dutch AP and its European counterparts show these are not empty threats. Authorities are actively investigating and penalising organisations that fail to meet their obligations. For more information on the specific role and powers of the Dutch authority, you can read our detailed article on the Dutch Data Protection Authority.
A powerful example of this is the recent action against Clearview AI. On September 3, 2024, the Dutch AP levied a €30.5 million fine against the American facial recognition company for its illegal data collection practices. This case hammers home the significant financial consequences of processing biometric information without a lawful basis. It's part of a broader trend across the EU, where data protection authorities have imposed fines totalling billions of euros. The most common and costly violation? An insufficient legal basis. You can explore more about the biggest GDPR fines and their causes.
Beyond Financial Penalties
The consequences of a GDPR violation extend far beyond the initial fine. The reputational damage can be even more costly and long-lasting. A public enforcement action can lead to a significant loss of trust from customers, partners, and the public.
Other potential consequences include:
- Corrective Orders: The AP can order you to stop processing data, forcing a halt to critical business operations.
- Data Deletion Mandates: You may be required to erase all improperly collected biometric data.
- Civil Litigation: Affected individuals have the right to seek compensation for damages, opening the door to class-action lawsuits.
Ultimately, the enforcement landscape in the Netherlands is robust. The Dutch AP has shown it will not hesitate to use its full powers to protect individuals' most sensitive data. This makes diligent biometric data GDPR compliance an essential business priority.
Creating Your Biometric Data Breach Response Plan

When biometric data is compromised, it's not just another IT problem; it's a full-blown crisis. You can't just 'reset' a fingerprint or an iris scan like you would a password. How your organisation acts in those first few hours is critical, not only for limiting the damage but for showing regulators you're accountable.
That’s why having a robust, pre-prepared incident response plan specifically for biometric data isn't just a good idea—it's essential. The moment you become aware of a breach, the clock starts ticking.
The 72-Hour Notification Deadline
Under the GDPR, you have a strict 72-hour window to report a personal data breach to your supervisory authority after you discover it. For any business operating in the Netherlands, this means notifying the Dutch Data Protection Authority (Autoriteit Persoonsgegevens, or AP).
Seventy-two hours is not a lot of time, which is exactly why a pre-planned response is so vital. Your notification must detail the nature of the breach, the types of data and approximate number of individuals affected, and the likely consequences. You also have to explain the measures you’ve already taken or plan to take.
Step 1: Contain the Breach and Assess the Impact
Your immediate priority is to stop the bleeding. This demands a coordinated effort between your IT security and legal teams to contain the threat and figure out precisely what happened.
- Isolate Affected Systems: Take compromised systems offline immediately to prevent any further unauthorised access or data exfiltration.
- Preserve Evidence: Secure all logs and digital evidence. This is crucial for a proper forensic investigation and for your regulatory reporting.
- Identify the Data: Get specific about what biometric data was affected. Was it raw images or encrypted templates? Who are the individuals involved?
Step 2: Determine if You Must Notify Individuals
Once you grasp the scope of the breach, you face another critical decision. The GDPR requires you to notify the affected individuals directly and "without undue delay" if the breach is likely to result in a high risk to their rights and freedoms.
With biometric data, this 'high risk' threshold is almost always met. A breach could lead to irreversible identity theft, financial fraud, or other significant personal harm. The Dutch AP has demonstrated increasingly strict enforcement of these notification requirements. During 2024, the authority received 37,839 personal data breach notifications, with a significant number triggering follow-up actions. The Dutch AP’s stance often diverges from other EU authorities, viewing most breaches as high-risk and therefore requiring direct notification to affected individuals. You can discover more insights about the Dutch DPA's approach to data breaches.
Your notification to individuals must be in clear and plain language. It should explain what happened, what information was involved, and what steps they can take to protect themselves, such as being vigilant for phishing attempts.
Step 3: Execute and Document Your Response
Your response plan should be a living playbook, not a document that gathers dust. As you execute the plan, document every single action taken. This documentation will become your primary evidence to the AP that you acted responsibly and diligently.
This includes logging every decision, communication, and technical measure from the moment of discovery. A well-documented response can significantly influence how regulators view your organisation's overall compliance and may impact the severity of any potential penalties.
Common Questions on Biometric Data Compliance
When you get down to the practicalities of using biometrics in the Netherlands, a lot of specific questions pop up. It’s one thing to understand the rules in theory, but another to apply them to real-world business scenarios. We've gathered some of the most common questions our clients ask to give you some clarity.
Can I Require Employees to Use a Biometric Time Clock?
In almost every situation in the Netherlands, the answer is a firm no. The Dutch AP takes the view that the relationship between an employer and an employee has an inherent power imbalance. Because of this, an employee’s consent can’t truly be considered ‘freely given’, which makes it an invalid legal basis for mandatory use.
To proceed, you’d have to prove a compelling and absolute necessity that couldn’t be met by any less invasive method. That’s an incredibly high bar to clear for something as straightforward as time tracking, and it's very unlikely to succeed.
Is Using Facial Recognition to Unlock a Company Phone a GDPR Risk?
Yes, this is definitely a GDPR risk if you don't manage it carefully. While it might feel like a simple convenience feature, you're still processing special category data.
The key here is where the data is stored. If the facial template is kept securely only on the device itself and never sent to a central company server, the risk is significantly lower. Even so, you must still carry out a DPIA, be completely transparent with your employee about how it works, and always offer a non-biometric alternative, like a good old-fashioned PIN or password.
How Long Can We Legally Store Biometric Data After an Employee Leaves?
You must get rid of it the moment it's no longer needed for its original purpose. For an access control system, this means the biometric template should be securely and permanently deleted on the employee’s last day, or very shortly thereafter.
There is simply no legitimate reason to hold onto this highly sensitive data once the employment relationship is over. Having a clear, automated deletion policy is a non-negotiable part of biometric data GDPR compliance.
At Law & More, our expert legal team can help you navigate the complexities of data protection law to ensure your business operations are fully compliant. For personalised advice on your specific situation, visit us at https://lawandmore.eu.
